blog
Hybrid Cloud PostgreSQL Deployment Tips
Hybrid Cloud is a common architecture design in any company. This concept combines public cloud, private cloud, and even on-premise solutions allowing companies to have flexibility on where to store and how to use their data. It also helps in implementing a High Availability environment. The problem is that deploying this kind of environment could be a hard and time-consuming task. In this blog, we will see what Hybrid Cloud is, some considerations to take into account before using it, and how to deploy this environment using ClusterControl.
What is Hybrid Cloud?
It is a topology that uses a mix of private, and public cloud, and even on-premises services. It sounds similar to a Multi-Cloud environment, but the main difference is that this concept refers to the combinations of public and private specifically, which could include on-prem too.
Hybrid Cloud Databases Considerations
The move to a Hybrid Environment is different for every company as they have their own unique set of data, requirements, limitations, and processes that go with it.
Let’s see some considerations to take into account when planning this kind of topology.
-
Compliance: Make sure to select a vendor that specializes in your industry and is familiar with the unique compliance measures that must be met whether that’s HIPAA, FISMA, PCI, or whatever regulations your company subscribes to. Ultimately your database management strategy should be determined by what architecture will best meet the needs of your business and scale with you as you grow.
-
Workloads: Every database has different workloads. Some of those will fare better in a public cloud, some on-prem, and some in a private cloud. Knowing your workload is essential to finding the best mix for your databases.
-
Management and Maintenance: A new environment means a new way to manage it and maintain the data. Make sure you have the right pieces and people in place to manage those new environments need to be determined before you make the jump.
How to Deploy PostgreSQL in a Hybrid Cloud Environment
We will assume you have a ClusterControl installation running and have already created two different Cloud Provider accounts, or one account if you are using Public and Private Cloud in the same Cloud Provider, or if you are using a combination of Cloud and On-prem environments.
Preparing Your Cloud Environment
First, you need to create your environment in your main Cloud Provider. In this case, we will use AWS with 2 PostgreSQL nodes:
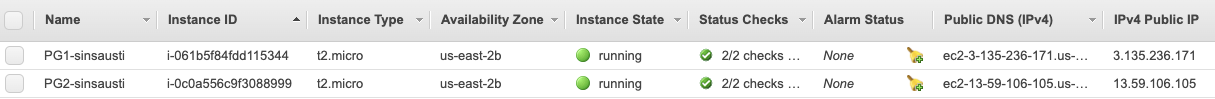
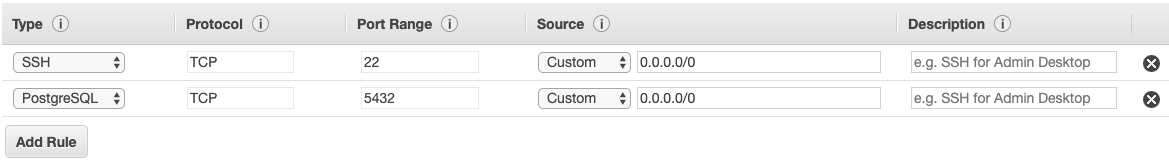
Make sure you have the SSH and PostgreSQL traffic allowed from your ClusterControl server by editing your Security Group:
Then, go to the secondary Cloud Provider, or to the Private or On-prem servers, and create at least one virtual machine that will be the standby node.
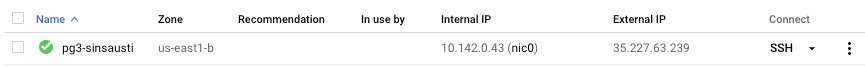
And again, make sure you are allowing SSH and PostgreSQL traffic from your ClusterControl server:
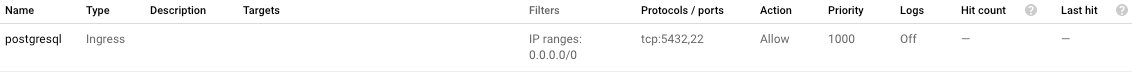
In this case, we are allowing the traffic without any restriction on the source, but it is just an example and it is not recommended in real life.
Deploying a PostgreSQL Cluster
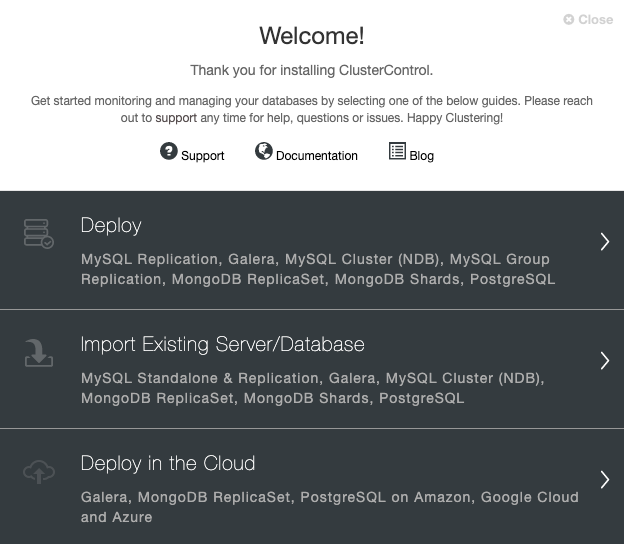
Go to your ClusterControl server, and select the option “Deploy”. If you already have a PostgreSQL instance running, then you need to select the “Import Existing Server/Database” instead.
When selecting PostgreSQL, you must specify User, Key or Password, and port to connect by SSH to your PostgreSQL nodes. You also need the name for your new cluster and if you want ClusterControl to install the corresponding software and configurations for you.
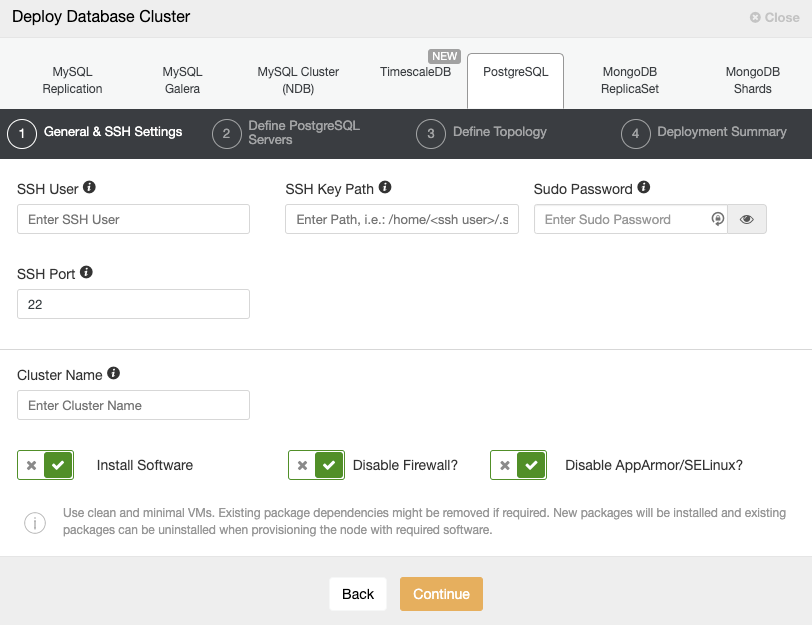
Please check the ClusterControl user requirements for more information about this step.
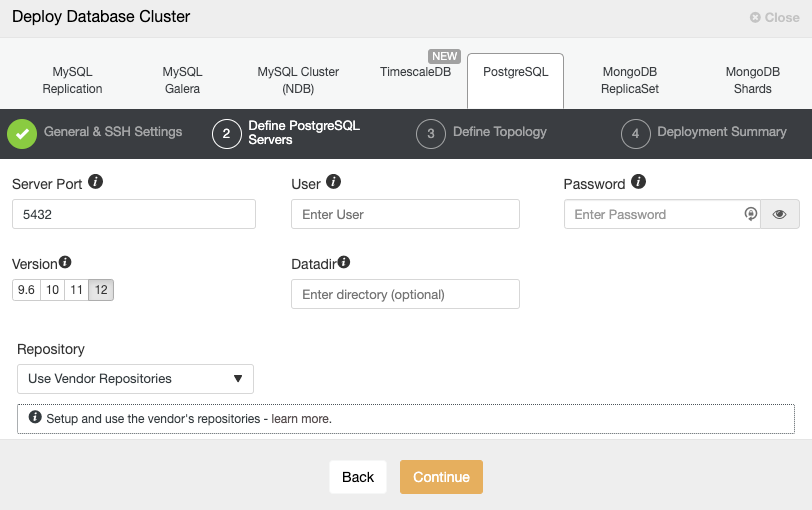
After setting up the SSH access information, you must define the database user, version, and datadir (optional). You can also specify which repository to use. In the next step, you need to add your servers to the cluster you are going to create.
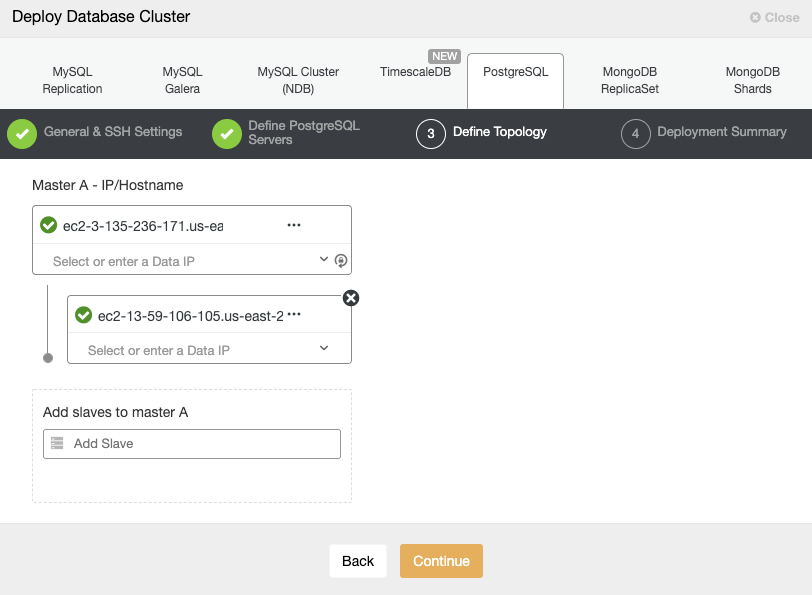
When adding your servers, you can enter IP or hostname. In this step, you could also add the node placed in the secondary Cloud Provider or on-prem, as ClusterControl doesn’t have any limitations about the network to be used, but to make it more clear, we will add it in the next section. The only requirement here is to have SSH access to the node.
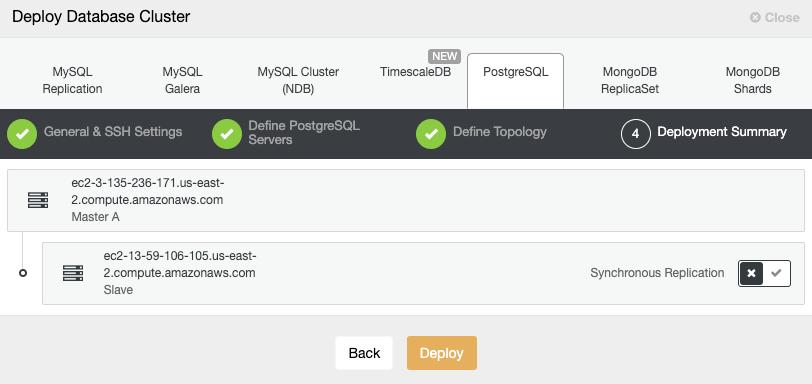
In the last step, you can choose if your replication will be Synchronous or Asynchronous.
In case you are adding your remote node here, it is important to use Asynchronous replication, if not, your cluster could be affected by the latency or network issues.
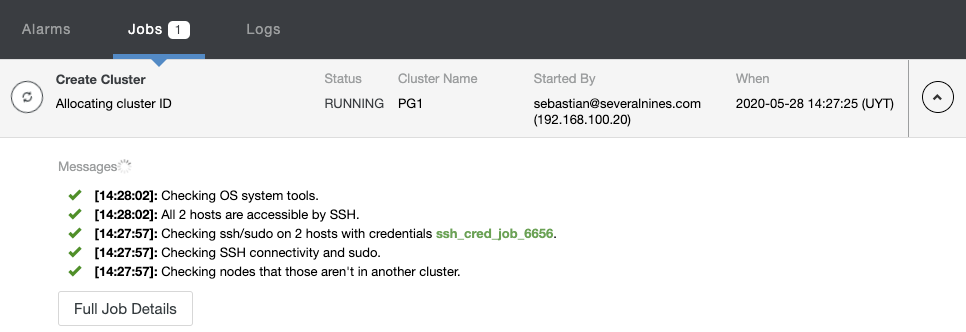
You can monitor the creation status in the ClusterControl activity monitor.
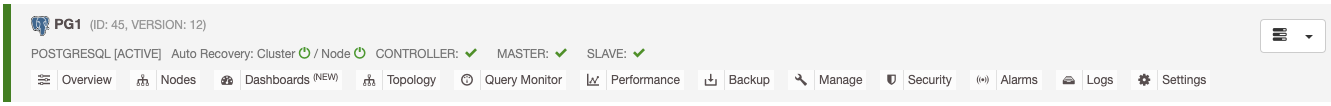
Once the task is finished, you can see your new PostgreSQL cluster in the main ClusterControl screen.
Adding a Remote Standby Node
Once you have your cluster created, you can perform several tasks on it, like deploy/import a load balancer or a replication node.
Go to cluster actions and select “Add Replication Slave”:
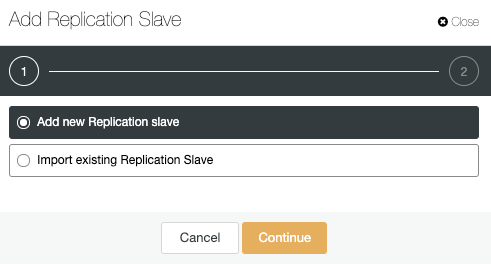
Let’s use the “Add new Replication slave” option as we are assuming that the remote node is a fresh installation, if not, you can use the “Import existing Replication Slave” option instead.
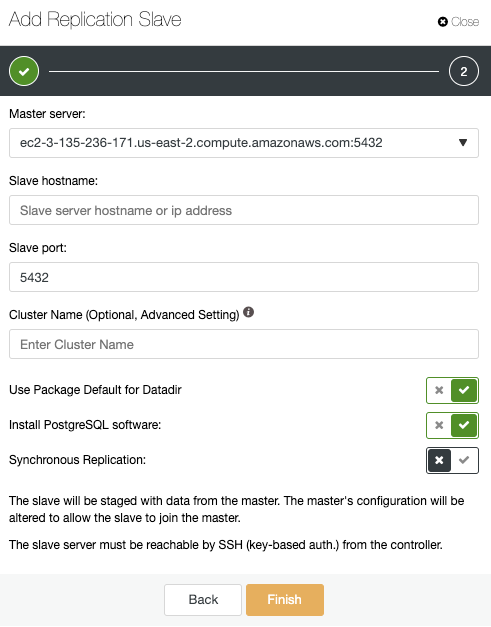
Here, you only need to choose your Primary server, enter the IP address for your new standby server, and the database port. Then, you can choose if you want ClusterControl to install the software and if the replication should be Synchronous or Asynchronous. Again, if you are adding a node in a different location (different cloud provider or on-prem) you should use Asynchronous replication to avoid issues related to the network performance.
In this way, you can add as many replicas as you want and spread read traffic between them using a load balancer, which you can also implement with ClusterControl.
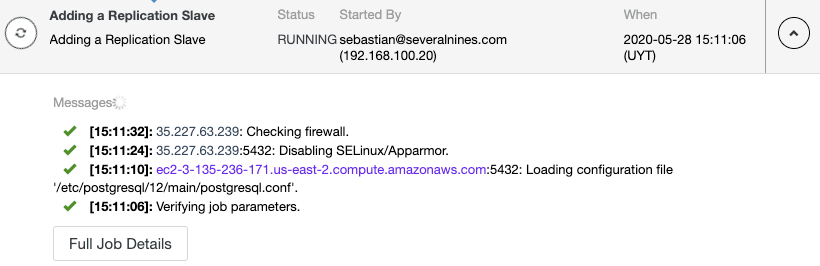
You can monitor the replication node creation in the ClusterControl activity monitor.
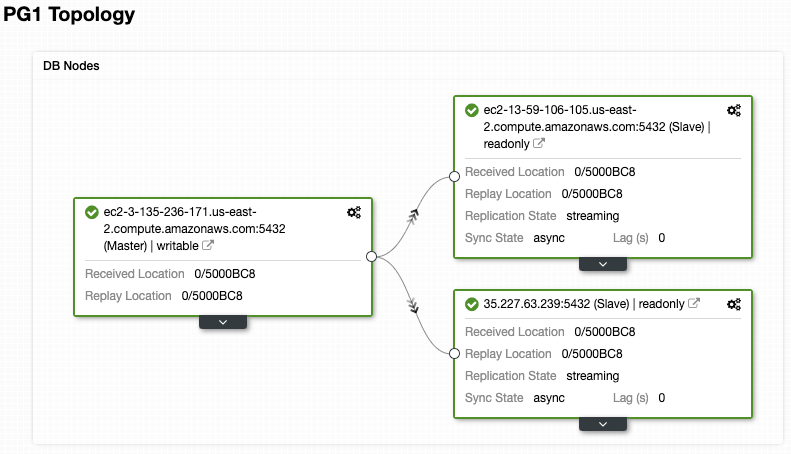
And check your final topology in the Topology View Section.
Conclusion
These ClusterControl features will allow you to quickly set up replication in a Hybrid Cloud environment, between different Cloud Providers, or even between a Cloud Provider and an On-prem environment, for a PostgreSQL database (and different technologies), and manage the setup in an easy and friendly way. About the communication between the Cloud Providers, or between Private and Public Cloud, for security reasons, you must restrict the traffic only from known sources, to reduce the risk of unauthorized access to your network.




