blog
An Introduction to Percona Server for MongoDB 4.2

When choosing a NoSQL database technology important considerations should be taken into account, such as performance, resilience, reliability, and security. These key factors should also be aligned with achieving business goals, at least as far as the database is concerned.
Many technologies have come into play to improve these aspects, and it is advisable for an organisation to improve the salient options and try integrating them into the database systems.
New technologies should ensure maximum performance to enhance achievement of business goals at an affordable operating cost but with more manipulative features such as error detection and alerting systems.
In this blog we will discuss the Percona version of MongoDB and how it expands the power of MongoDB in a variety of ways.
What is Percona Server for MongoDB?
For a database to perform well, there must be an optimally established underlying server for enhancing read and write transactions. Percona Server for MongoDB is a free open-source drop-in replacement for the MongoDB Community Edition, but with additional enterprise-grade functionality. It is designed with some major improvements on the default MongoDB server setup.
It delivers high performance, improved security, and reliability for optimum performance with reduced expenditure on proprietary software vendor relationships.
Percona Server for MongoDB Salient Features
MongoDB Community Edition is core to the Percona server considering that it already constitutes important features such as the flexible schema, distributed transactions, familiarity of the JSON documents and native high availability. Besides this, Percona Server for MongoDB integrates the following salient features that enables it to satisfy the aspects we have mentioned above:
- Hot Backups
- Data at rest encryption
- Audit Logging
- Percona Memory Engine
- External LDAP Authentication with SASL
- HashiCorp Vault Integration
- Enhanced query profiling
Hot Backups
Percona server for MongoDB creates a physical data backup on a running server in the background without any noticeable operation degradation. This is achievable by running the createBackup command as an administrator on the admin database and specifying the backup directory.
> use admin
switched to db admin
> db.runCommand({createBackup: 1, backupDir: "/my/backup/data/path"})
{ "ok" : 1 }When you receive { “ok” : 1 } then the backup was successful. Otherwise, if for example you specify an empty backup directory path, you may receive an error response i.e:
{ "ok" : 0, "errmsg" : "Destination path must be absolute" }Restoring the backup requires one to first stop the mongod instance, clean the data directory, copy the files from the directory and then restart the mongod service. This can be done by running the command below
$ service mongod stop && rm -rf /var/lib/mongodb/* && cp --recursive /my/backup/data/path /var/lib/mongodb/ && service mongod startYou can also store the backup in archive format if using Percona server for MongoDB 4.2.1-1
> use admin
> db.runCommand({createBackup: 1, archive: "path/to/archive.tar" })You can also backup directly to AWS S3 using the default settings or with more configurations. For a default S3 bucket backup:
> db.runCommand({createBackup: 1, s3: {bucket: “backup”, path: “newBackup”}})
Data-at-Rest Encryption
MongoDB version 3.2 introduced data at rest encryption for the WiredTiger storage engine towards ensuring that data files can be decrypted and read by parties with decryption key only. Data encryption at rest in Percona Server for MongoDB was introduced in version 3.6 to go in hand with data encryption at rest interface in MongoDB. However the latest version does not include support for Amazon AWS and KIMP key management services.
The encryption can also be applied to rollback files when data at rest is enabled. Percona Server for MongoDB uses encryptionCipherMode option with 2 selective cipher modes:
- AES256-CBC (default cipher mode)
- AES256-GCM
You can encrypt data with the command below
$ mongod ... --encryptionCipherMode or
$ mongod ... --encryptionCipherMode AES256-GCMWe use the –ecryptionKeyFile option to specify the path to a file that contains the encryption key.
$ mongod ... --enableEncryption --encryptionKeyFile Audit Logging
For every database system, administrators have a mandate to keep track on activities taking place. In Percona Server for MongoDB, when auditing is enabled, the server generates an audit log file than constitutes information about different user events such as authorization and authentication. However, starting the server with auditing enabled, the logs won’t be displayed dynamically during runtime.
The Audit Logging in MongoDB Community Edition can take two data formats that is, JSON and BSON. However, for Percona Server for MongoDB, audit logging is limited to JSON file only. The server also logs only important commands contrary to MongoDB that logs everything. Since the filtering procedure in Percona is so unclear in terms of the filtering syntax, enabling the audit log without filtering would offer more entries from which one can narrow down to own specifications.
Percona Memory Engine
This is a special configuration of the WiredTiger storage engine that does not store user data on disk. The data fully resides and is readily available in the main memory except for diagnostic data that is written to disk. This makes data processing much faster but with a consideration that you must ensure there is enough memory to hold the data set and the server should not shut down. One can select a storage engine to use with the –storageEngine command. Data created for one storage engine cannot be compatible with other storage engines because each storage engine has its own data model. For instance to select the in-memory storage engine. You first stop any running mongod instance and then issue the commands:
$ service mongod stop
$ mongod --storageEngine inMemory --dbpath If you already have some data with your default MongoDB Community edition and you would like to migrate to Percona Memory Engine, just use the mongodumb and mongorestore utilities by issuing the command:
$ mongodump --out
$ service mongod stop
$ rm -rf /var/lib/mongodb/*
$ sed -i '/engine: .*inMemory/s/#//g' /etc/mongod.conf
$ service mongod start
$ mongorestore External LDAP Authentication With SASL
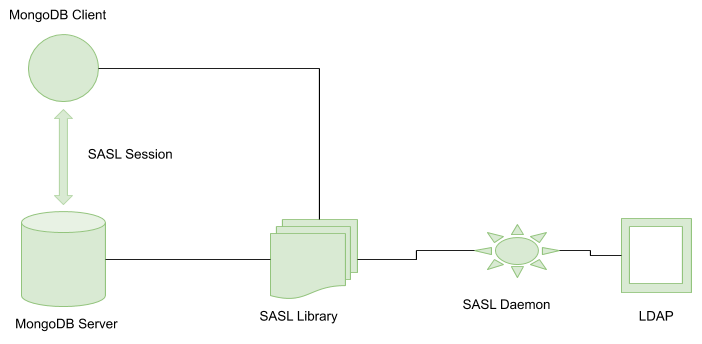
Whenever clients make either a read or write request to MongoDB mongod instance, they need to authenticate against the MongoDB server user database first. The external authentication allows the MongoDB server to verify the client credentials (username and password) against a separate service. The external authentication architecture involves:
- LDAP Server which remotely stores all user credentials
- SASL Daemon that is used as a MongoDB server-local proxy for the remote LDAP service.
- SASL Library: creates necessary authentication data for MongoDB client and server.
Authentication session sequence
- The Client gets connected to a running mongod instance and creates a PLAIN authentication request using the SASL library.
- The auth request is then sent to the server as a special Mongo command which is then received by the mongod server with its request payload.
- The server creates some SASL sessions derived with client credentials using its own reference to the SASL library.
- The mongod server passes the auth payload to the SASL library which hands it over to the saslauthd daemon. The daemon passes it to the LDAP and awaits a YES or NO response upon the authentication request by checking if the user exists and the submitted password is correct.
- The saslauthd passes this response to the mongod server through the SASL library which then authenticates or rejects the request accordingly.
Here is an illustration for this process:
To add an external user to a mongod server:
> db.getSiblingDB("$external").createUser( {user : username, roles: [ {role: "read", db: "test"} ]} );External users however cannot have roles assigned in the admin database.
HashiCorp Vault Integration
HashCorp Vault is a product designed to manage secrets and protect sensitive data by securely storing and tightly controlling access to confidential information. With the previous Percona version, data at rest encryption key was stored locally on the server inside the key file. The integration with HashCorp Vault secures the encryption key much far better.
Enhanced Query Profiling
Profiling has a degradation impact on the database performance especially when there are so many queries issued. Percona server for MongoDB comes in hand by limiting the number of queries collected by the database profiler hence decreases its impact on performance.
Conclusion
Percona Server for MongoDB is an enhanced open source and highly scalable database that may act as a compatible drop-in replacement for MongoDB Community Edition but with similar syntax and configuration. It enhances extensive data security especially one at rest and improved database performance through provision of Percona Server engine, limiting on the profiling rate among other features.
Percona Server for MongoDB is fully supported by ClusterControl as an option for deployment.




