Severalnines Blog
Today, we're asking PostgreSQL to do more and more, like handling both transactions and analytics, powering huge SaaS platforms, managing event data, and even dipping into AI-related tasks like vector search. This intense pressure highlights some pain points: slow, unpredictable reads, rigid indexing, complex setups, and risky major upgrades. PostgreSQL...
- AI
- Backup Management
- Cloud
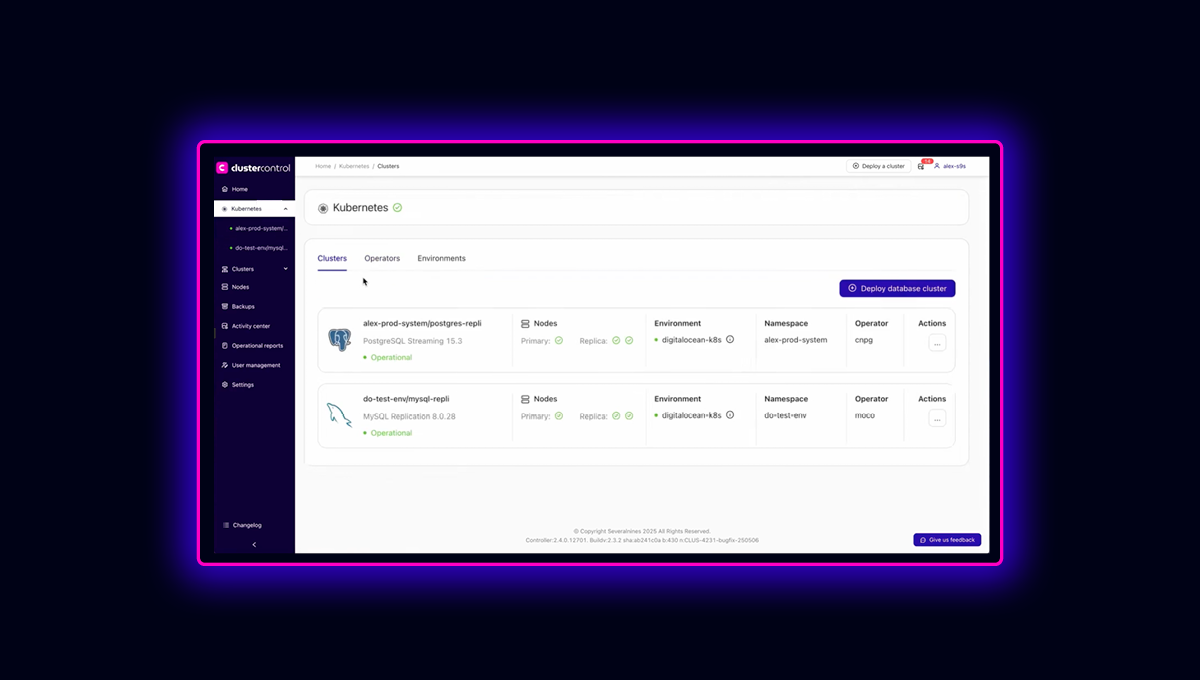
- ClusterControl
- Configuration Management
- Database - General
- DBaaS
- Deployment & Scaling
- Disaster recovery
- Hybrid Operations
- Hybrid-cloud
- Industry News & Events
- Logging
- Monitoring & Alerting
- Multi-cloud
- Operational Reporting
- Performance Management
- Podcast
- Recovery & Repair
- Security & Compliance
- Sovereign DBaaS
- Upgrades & Patches
ClusterControl
The best of DBaaS news, delivered to your inbox
Before we dive deep into the fascinating world of PostgreSQL Logical and Bi-Directional Replication (BDR), let's take a quick moment to look at multi-tenancy and multi-cloud strategies. Setting the stage for today’s cloud operating model, it was common to administer and host databases in a multi-tenant setup, where a physical...