blog
Oracle’s Ironclad Autonomous Database

NEWS ALERT: “The Marriott just revealing a massive data breach involving guest reservation database at its Starwood brand. Marriott says it was unauthorized access since 2014. This includes up to 500 million guests… For approximately 327 million of these guests, the information that was exposed includes a combination of name, mailing address, phone number, email address, you ready for this – passport number… Starwood preferred guest account information, date of birth, gender, arrival and departure information… including reservation dates and communication preference. As you know, when you go to a hotel, especially internationally, they take your passport. Often times, they take a copy of your passport.”– CNBC News Report
This is a real excerpt given by a CNBC News reporter in 2018. It took Marriott’s technical team almost four years to detect the breach of their system. The damages? It has been estimated to be between $200 and $600 million dollars.
Unfortunately, these types of reports are becoming all too common. When a hacker wants to breach a system, they use botnets to increase the success of their criminal activity. These internet-connected private computers are equipped with malicious software and are used to steal personal data.
Most of the time, they are acting for financial gain. In rare cases, attacks are performed to retrieve highly classified information. The motive for the attack is determined only after analysts track precisely what the data has been used for. If the data does not show up on the dark web, there is a high probability that nation-states executed the breach.
Regulatory requirements have become more demanding but fail to slow down cybercriminals. The 2019 Data Breach Report revealed additional shocking results. Hackers have been able to successfully infiltrate systems due to a broad range of root causes.
The causes of these security breaches include, but are not limited to:
- Organizations Failing to Implement Security Patches
- Social Engineering Attacks
- Human Error
- Downloading Malware
- Misuse by Authorized Users
To prevent these intrusions, organizations rely heavily on database administrators (DBA) to perform critical daily tasks. However, network penetrations are still on the rise. If you ponder over the statement mentioned above, it does not make any sense. I’ll repeat it. To prevent these intrusions, organizations rely heavily on database administrators (DBA) to perform critical daily tasks. Again, human error is part of this massive problem. But how can this be? Utilizing DBAs to prevent cyber attacks has been used for decades.
Everyone knows that computers can complete computations at a high rate of speed, 24 hours a day until a system has been successfully infiltrated. It’s virtually impossible for anyone to secure and maintain a database under these conditions. The expectation for a human being to compete with the performance of a malicious computer is not reasonable unless you are on the other end to pull the plug. To put up the best defense against cybercriminals, you must use a computer to defend your network against a computer.
The Oracle Autonomous Database does just that.
The Database That Uses Machine Learning
To grasp full knowledge of the Autonomous Database, you must understand its infrastructure. New hardware and software have been carefully crafted to meet the needs of database users. Oracle has established an advanced network of dedicated computers to protect the parameter of their cloud, in addition to each customer zone. This prevents the malicious activity of one customer from spreading to another customer using the Oracle service. Therefore, each customer will receive the highest level of protection.
The database itself is made up of two separate products that seamlessly work together to generate the highest level of performance. The Autonomous Data Warehouse (ADW) manages analytic workloads, which systematically stores data on metrics and performance. The Autonomous Transaction Processing (ATP)manages mixed workloads,which oversees the activity of business transactions. Combined together, each product plays a critical role in the function of the system.
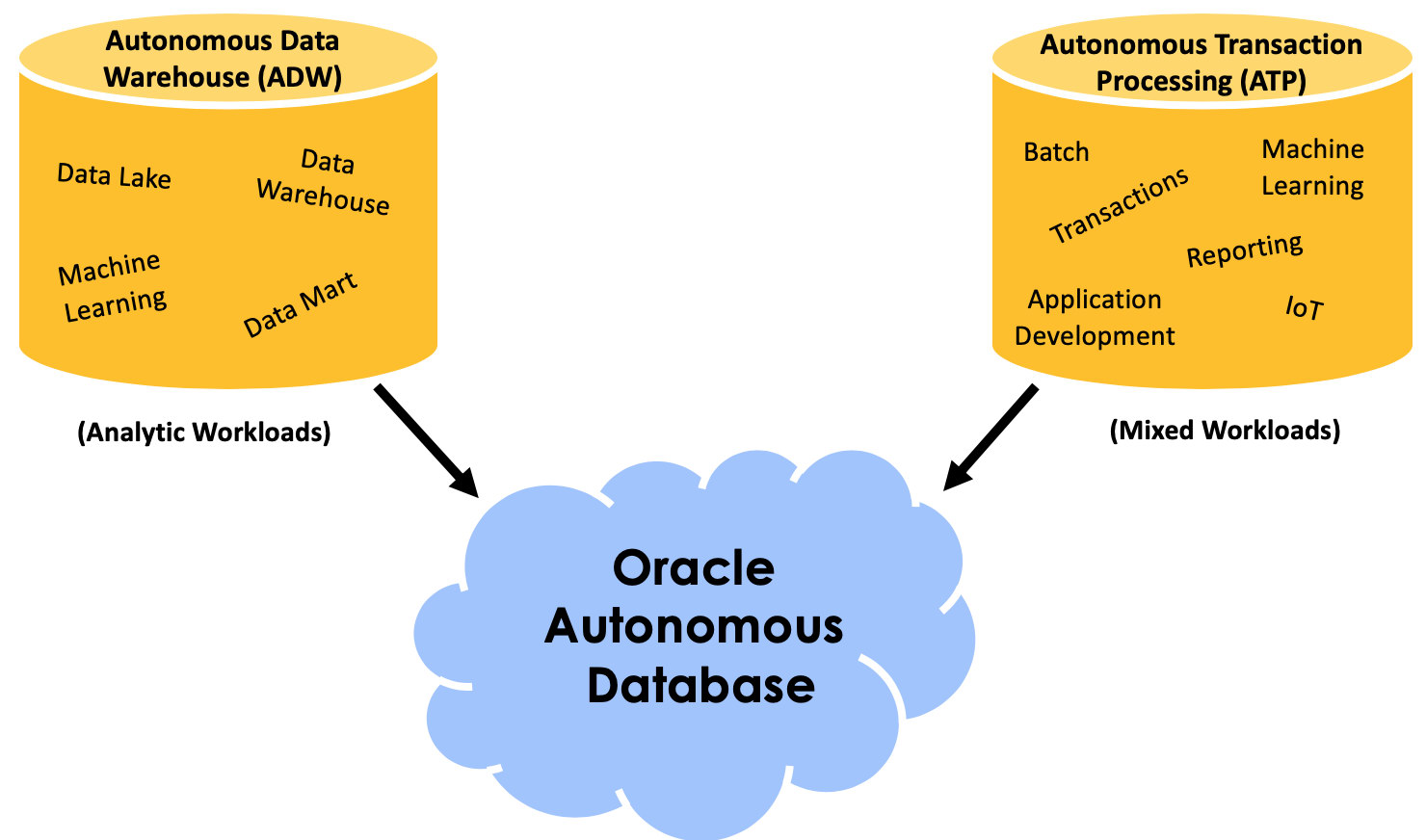
As you can see from figure one, both ADW and ATP include an exciting element called machine learning. It’s a branch of general artificial intelligence that’s modeled after the human brain. Computer scientists take a sizable amount of data and upload it to the neural network. Using that data as its base for accurate database performance, the computer will be able to identify patterns and make highly accurate predictions. These predictions can be used to make business decisions and increase revenue.
The database can also monitor and detect unusual activity within the system, even if the event is something the computer has never seen before. Abnormal events will be automatically flagged for further analysis. After careful inspection of the event, the machine will decide if access should be granted, or if it should be revoked to maintain the security of the system. If a manual database alteration causes an increase in vulnerability, the system will automatically take steps to correct the human error. As time goes on, the database becomes more secure because it will be comprised of a larger volume of accurate data.
Apache Zeppelin SQL Notebook is the back-end technology that allows for data processing to occur, and it is bundled with the ADW cloud service. Information is collected and displayed in the form of tables and charts for further analysis. Data scientists can then work together to review fraudulent transactions, analyze customer statistics, and gain access to the machine learning algorithms that are embedded with the service.
Key Features of the Apache Zeppelin SQL Notebook include:
- System Tutorials for Ease of Use
- Access to Shared Scheduler, Permissions, & Pre-Built Templates
- Individual & Shared Access to SQL Notebooks
- Scripting Language Assistance
- Access to Machine Learning Algorithms
Ultimately, machine learning gives this database the ability to inspect large quantities of data, learn from it with no human interference, and modify system activities to stop cyber criminal’s dead in their tracks. While your typical database requires downtime for events activities, the Autonomous Database does not. The system can automatically monitor, scale, tune, upgrade, and installs the security patches. The encryption of data in transit and at rest is enabled by default.
The Collaboration of Human and Machine
Even though the database is automated, the security of the database is a combination of machine learning and human implementation. It’s a shared responsibility because each DBA must provide ensure they are entering the appropriate information for each user. The role each user is assigned plays a large part in the level of access that is granted.
When a user severs ties with the organization, the DBA should act swiftly to revoke access to maintain security. If these critical steps are not executed appropriately, the organization will be at risk of experiencing a data breach.
It’s essential to test the security of your system before a hacker does it for you. However, it can be challenging to measure the level of protection your system has, especially after a DBA completes manual changes. Oracle has equipped their system with a Database Security Assessment Tool (DBSAT). It’s a free application that analyzes the database and provides a detailed report on how secure your system is. The report also includes an analysis of user privileges based on their job description and configuration settings.
Security should always be a top priority for any business. It only takes one data breach for customers to lose their trust in the company, and discontinue association. As a result, a loss in business revenue will be unavoidable. Large businesses will typically see a significant drop in the stock market, while small businesses will be forced to close their doors. The risk is simply too great. Take advantage of the highest level of database security and go autonomous.




