blog
How to Encrypt Hybrid Cloud Database Traffic

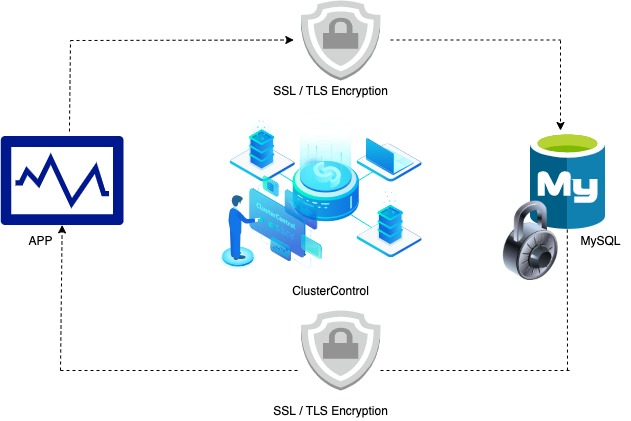
A secure database environment is hard to achieve, but extremely important in order to avoid data breaches, ransomware and other malicious activity. Security of data is a top priority from a business standpoint. When running in a private datacenter, your network is usually the first layer of defense. But in a distributed hybrid database cloud environment, where internal parts of the database topology as well as applications are distributed across datacenters, the network represents a bigger attach surface. Encryption of in-transit data traffic is one of the common measures to protect against network eavesdropping. In this blog we will see how we can encrypt hybrid cloud mysql database traffic.
Why do we Need to Encrypt Database Traffic?
The main reason is connections between database instances and any client applications should be encrypted, and ensure only authorized communication. This security layer can prevent unwanted sensitive data leak, or exclude the possibility for any SQL injection attack etc. Data in-transit can also mean the replication traffic between the database nodes, or traffic between load balancers/proxies and the database instances.
Activating SSL on MySQL Nodes
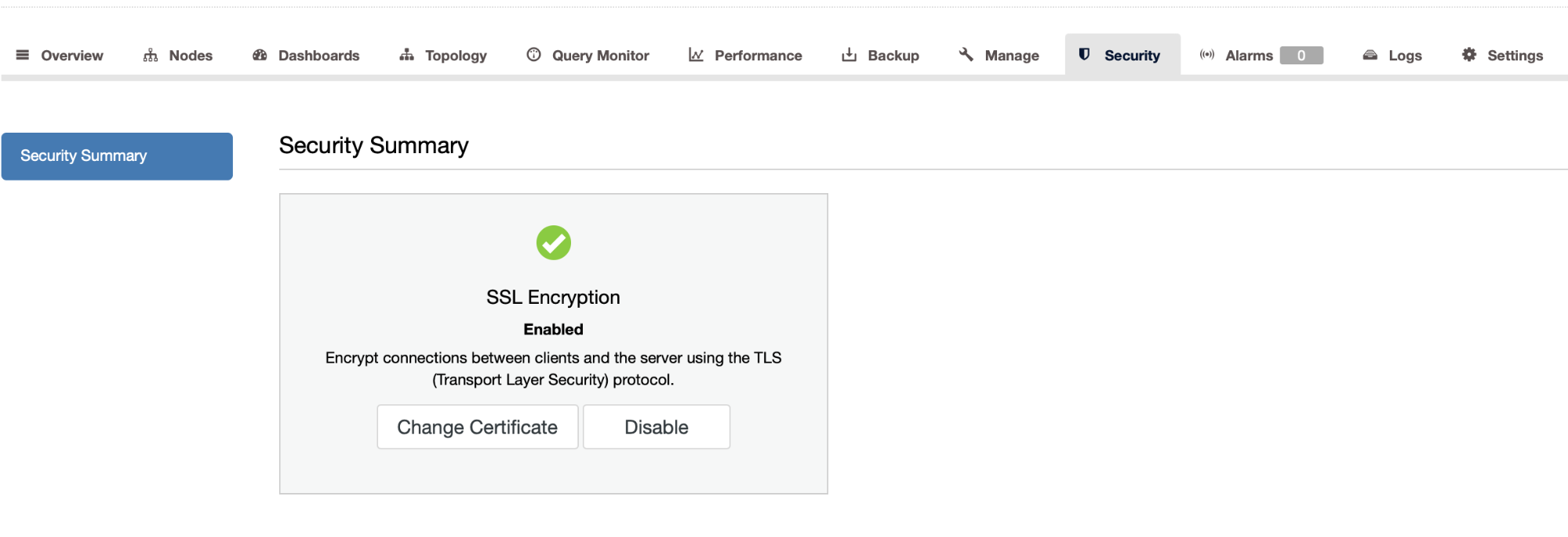
Newer versions of MySQL come with self-signed certificates and SSL enabled. On the other hand, if you would like to add another layer of security, you may want to use your own certificates, ClusterControl allows you to change the SSL certificate. In this blog, we explained how to do this using ClusterControl.
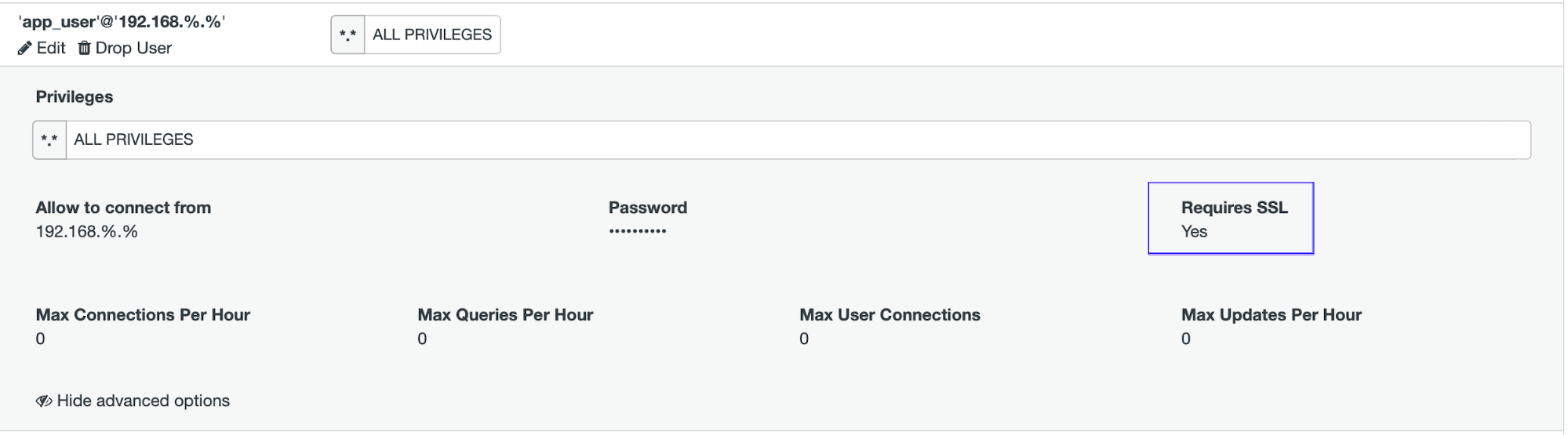
Activating SSL on Clients
MySQL performs encryption on a per-connection basis, and use of encryption for a given user can be optional or mandatory. To connect to the mysql nodes through SSL, ensure you have set up the user’s grant with “REQUIRE SSL” syntax, similar to below:
mysql> create user 'app_user'@'192.168.%.%' identified by 'R00t@123' REQUIRE SSL;
Query OK, 0 rows affected (0.00 sec)
mysql> grant all on *.* to 'app_user'@'192.168.%.%';
Query OK, 0 rows affected (0.00 sec)
This enables you to choose an encrypted or unencrypted connection according to the requirements of individual applications.
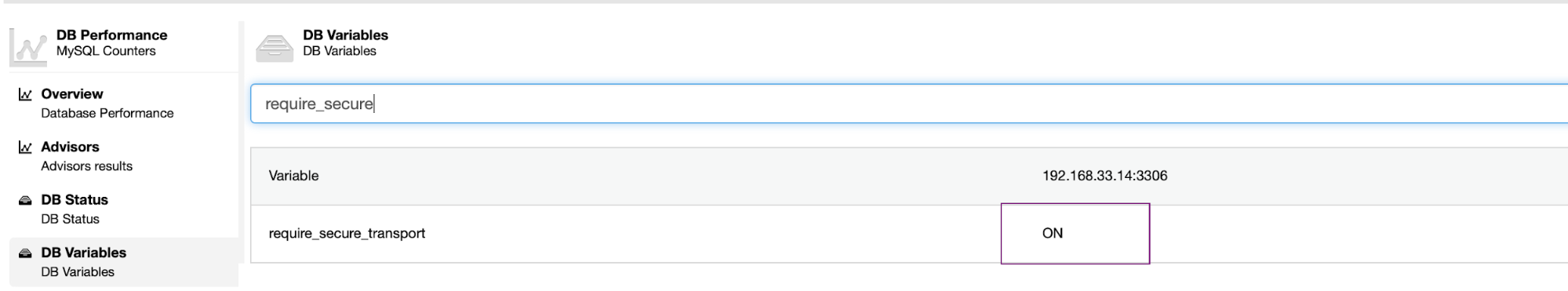
To ensure that clients are required to use encrypted connections, we need to enable the “require_secure_transport” parameter in my.cnf file. By default this parameter is OFF.
Verifying DB Connections
By default, mysql client attempts to establish an encrypted connection if the server supports encrypted connections, with further control available through the –ssl-mode option for example,
[root@centos11 vagrant]# mysql -u app_user -p -h 192.168.xx.xx -P3306 --ssl=1 -e "status;" | grep -i SSL
SSL: Cipher in use is ECDHE-RSA-AES256-GCM-SHA384
The SSL protocol uses different encryption algorithms to ensure the data received over the public and private networks. It has mechanisms to detect any data change or loss.
[root@centos11 vagrant]# mysql -u app_user -p -h 192.168.xx.xx -P3306 --ssl=1
Welcome to the MariaDB monitor. Commands end with ; or g.
Your MySQL connection id is 12656
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or 'h' for help. Type 'c' to clear the current input statement.
MySQL [(none)]> SHOW SESSION STATUS LIKE 'Ssl_cipher';
+---------------+-----------------------------+
| Variable_name | Value |
+---------------+-----------------------------+
| Ssl_cipher | ECDHE-RSA-AES256-GCM-SHA384 |
+---------------+-----------------------------+
1 row in set (0.00 sec)
MySQL [(none)]> show status like 'Ssl_version';
+---------------+---------+
| Variable_name | Value |
+---------------+---------+
| Ssl_version | TLSv1.2 |
+---------------+---------+
1 row in set (0.00 sec)Conclusion
Encrypting a database connections is not and should not a big deal, it is done by default in some of the newer versions of MySQL. As database security becomes an increasingly business and regulatory concern, there is a lot more to think about than just in-transit data encryption to secure your hybrid cloud environment. It is important to keep in mind that other layers of security apply when hosting a database, such as network and operating system security.