blog
Securing Your MySQL Installation

Requires ClusterControl 1.2.11 or later. Applies to MySQL based clusters.
During the life cycle of Database installation it is common that new user accounts are created. It is a good practice to once in a while verify that the security is up to standards. That is, there should at least not be any accounts with global access rights, or accounts without password.
Using ClusterControl, you can at any time perform a security audit.
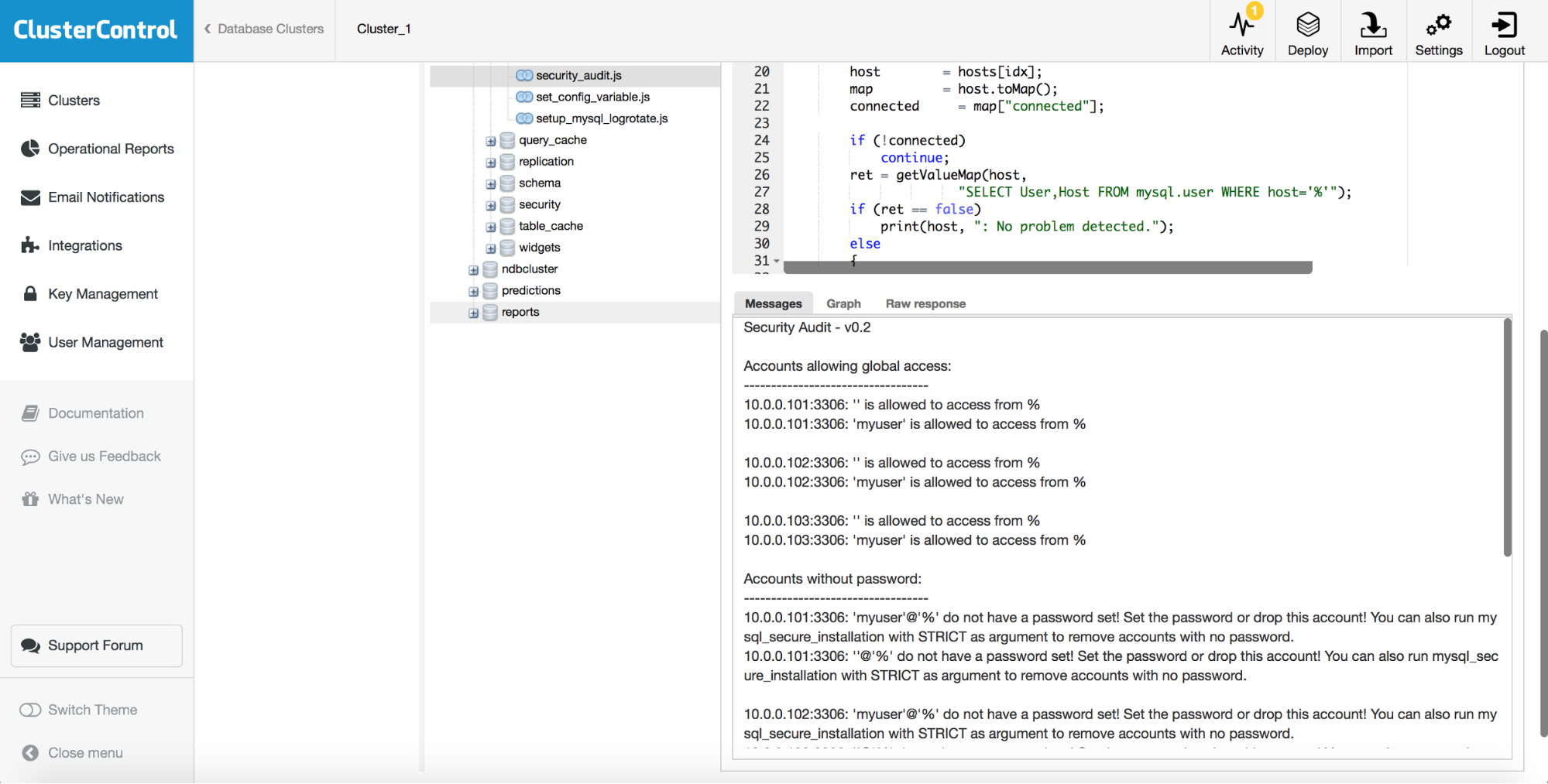
In the User Interface go to Manage > Developer Studio. Expand the folders so that you see s9s/mysql/programs. Click on security_audit.js and then press Compile and Run.
If there are problems you will clearly see it in the messages section:
Enlarged Messages output:
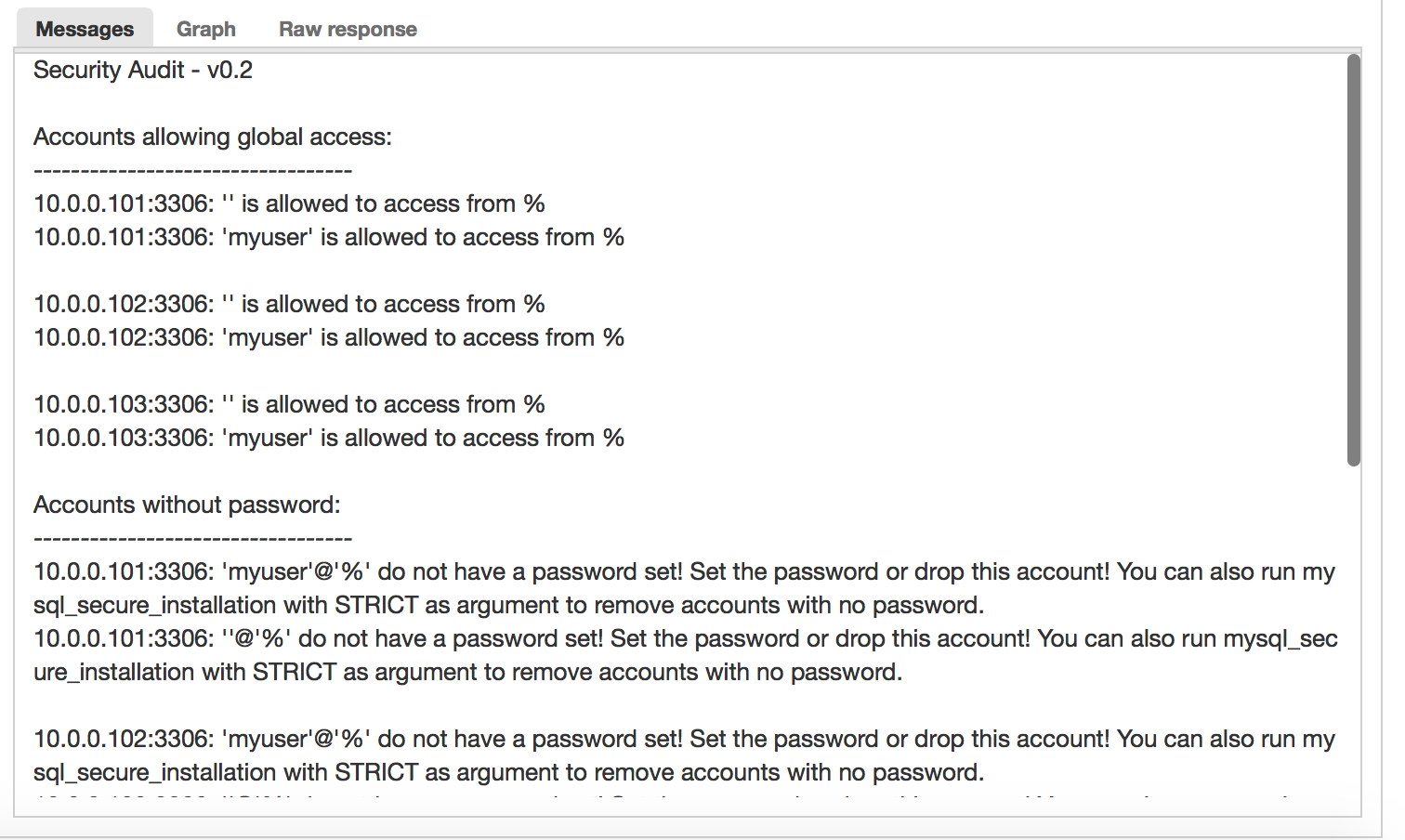
Here we have accounts that can connect from any hosts and accounts which do not have a password. Those accounts should not exist in a secure database installation. That is rule number one. To correct this problem, click on mysql_secure_installation.js in the s9s/mysql/programs folder.
Click on the dropdown arrow next to Compile and Run and press Change Settings. You will see the following dialog and enter the argument “STRICT”:
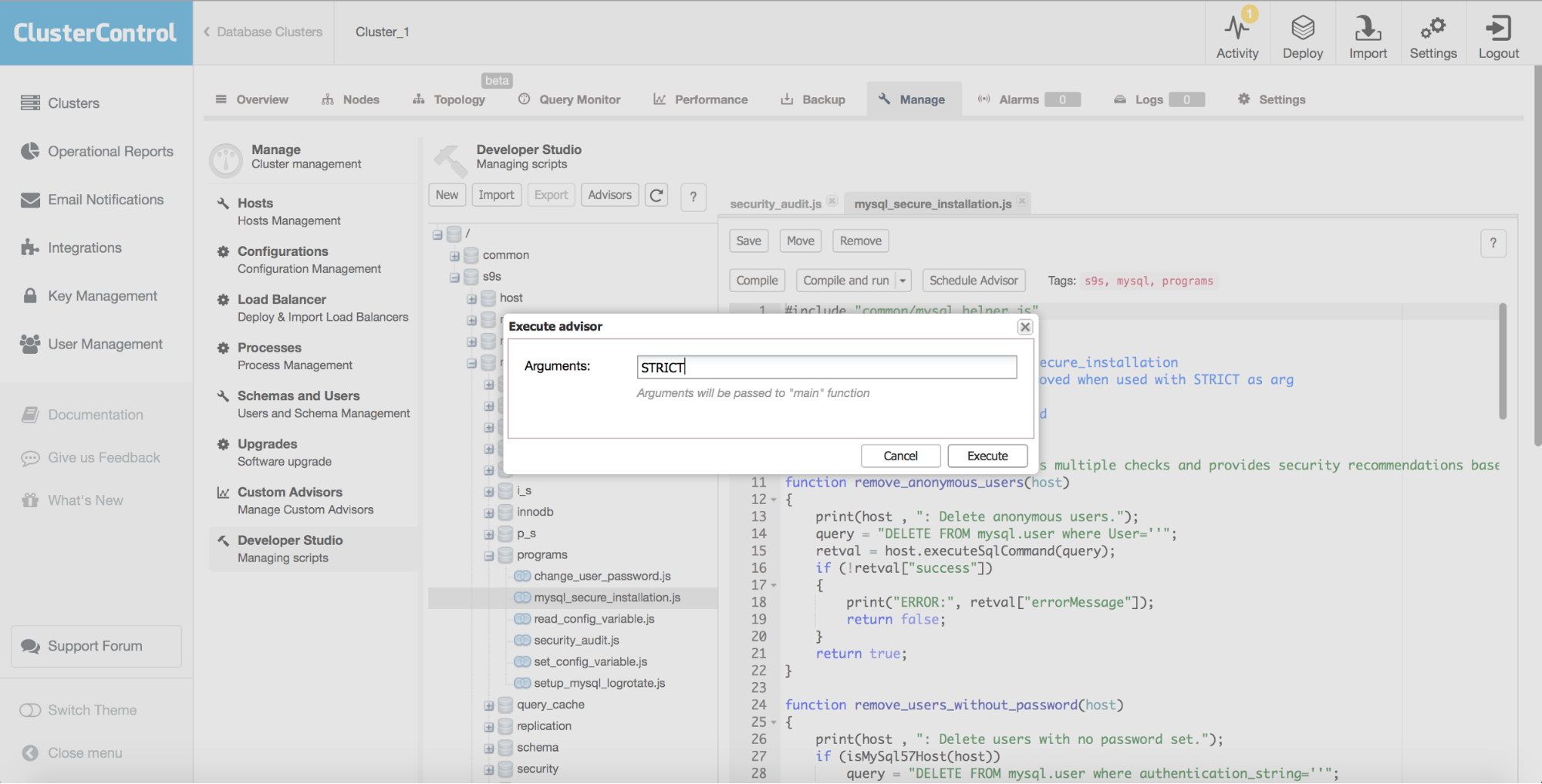
Then press Execute. The mysql_secure_installation.js script will then do on each MySQL database instance part of the cluster:
- Delete anonymous users
- Dropping ‘test’ database (if exists).
- If STRICT is given as an argument to mysql_secure_installation.js it will also do:
- Remove accounts without passwords.
In the Message box you will see:
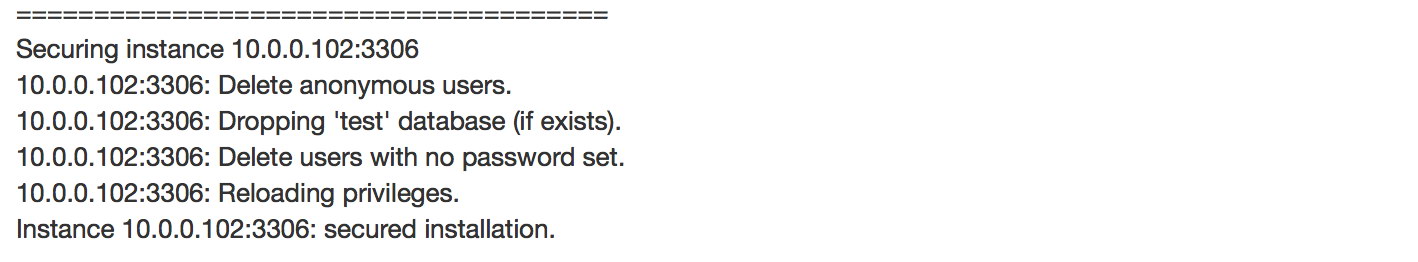
The MySQL database servers part of this cluster have now been secured and you have reduced the risk of compromising your data.
You can re-run security_audit.js to verify that the actions have had effect.
Happy Clustering!
PS.: To get started with ClusterControl, click here!




